AI-Driven Performance Testing
Simulate production-like conditions, test complete user flows, generate GDPR-safe data, and run continuous 24/7 validation — without replacing anything in your stack.
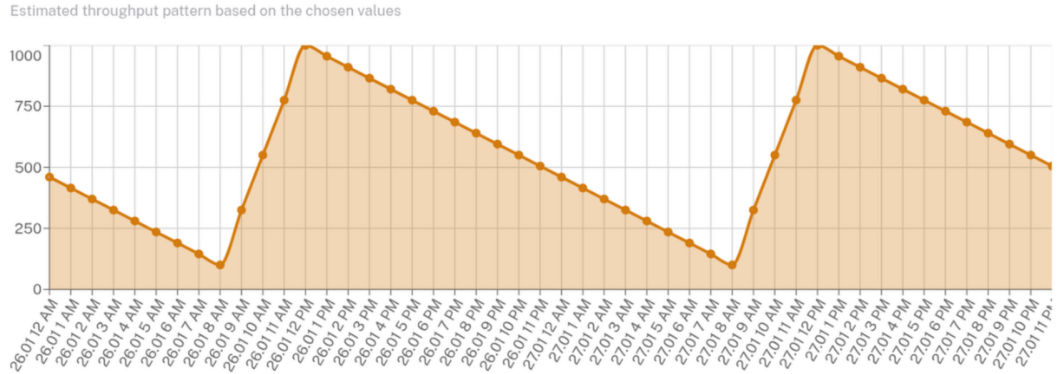
Traffic Simulation
Real traffic is never flat. Peak hours, holiday surges, gradual ramps — DeepXplore models production-like curves so your autoscalers and infrastructure are validated against conditions that actually mirror production. Constant-rate testing misses the bugs that matter.
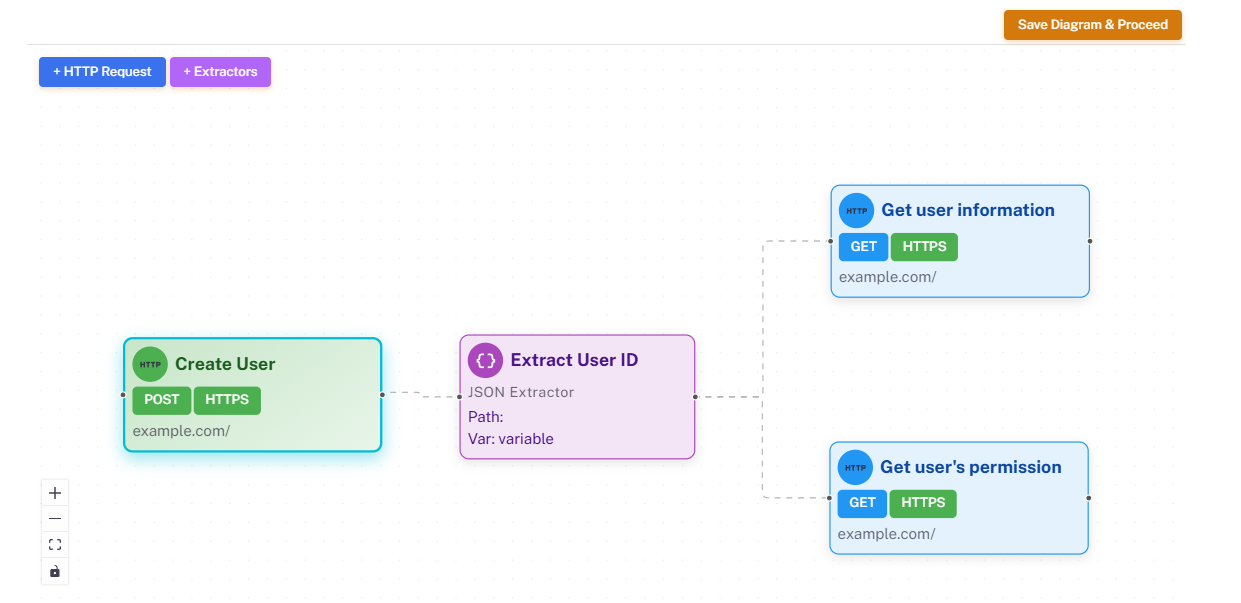
User Journey Testing
Real users don't call a single API — they browse, add to cart, check out, and pay. DeepXplore chains requests into full stateful journeys with automatic data extraction between steps, turning isolated endpoint tests into true system-level validation.
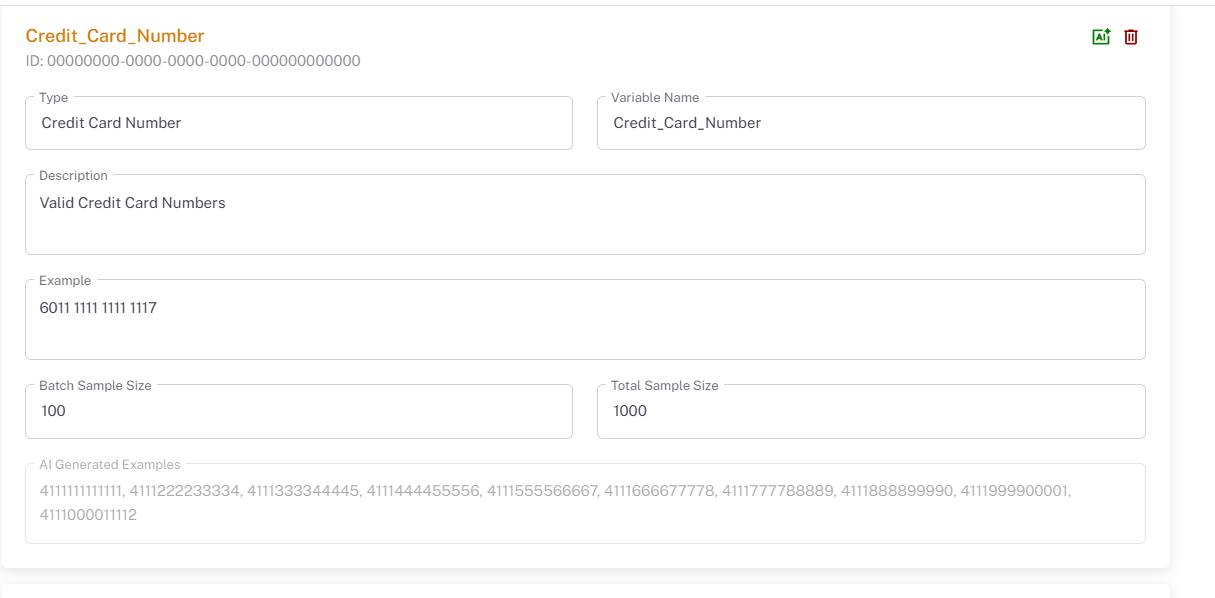
Intelligent Test Generation
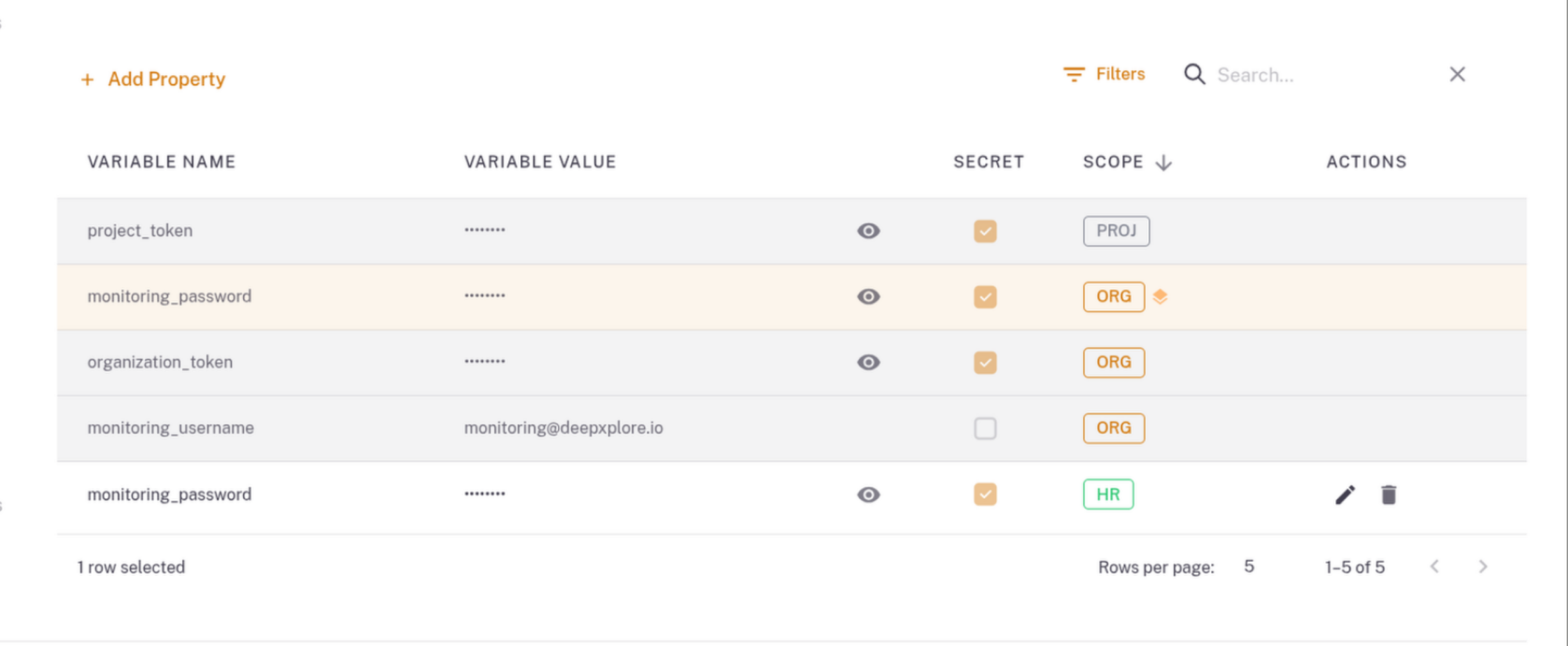
Import your OpenAPI specifications and DeepXplore automatically generates comprehensive test scenarios with distribution-aware synthetic data — from GDPR-safe customer profiles to sanction-list edge cases — so your tests reflect reality, not random noise.
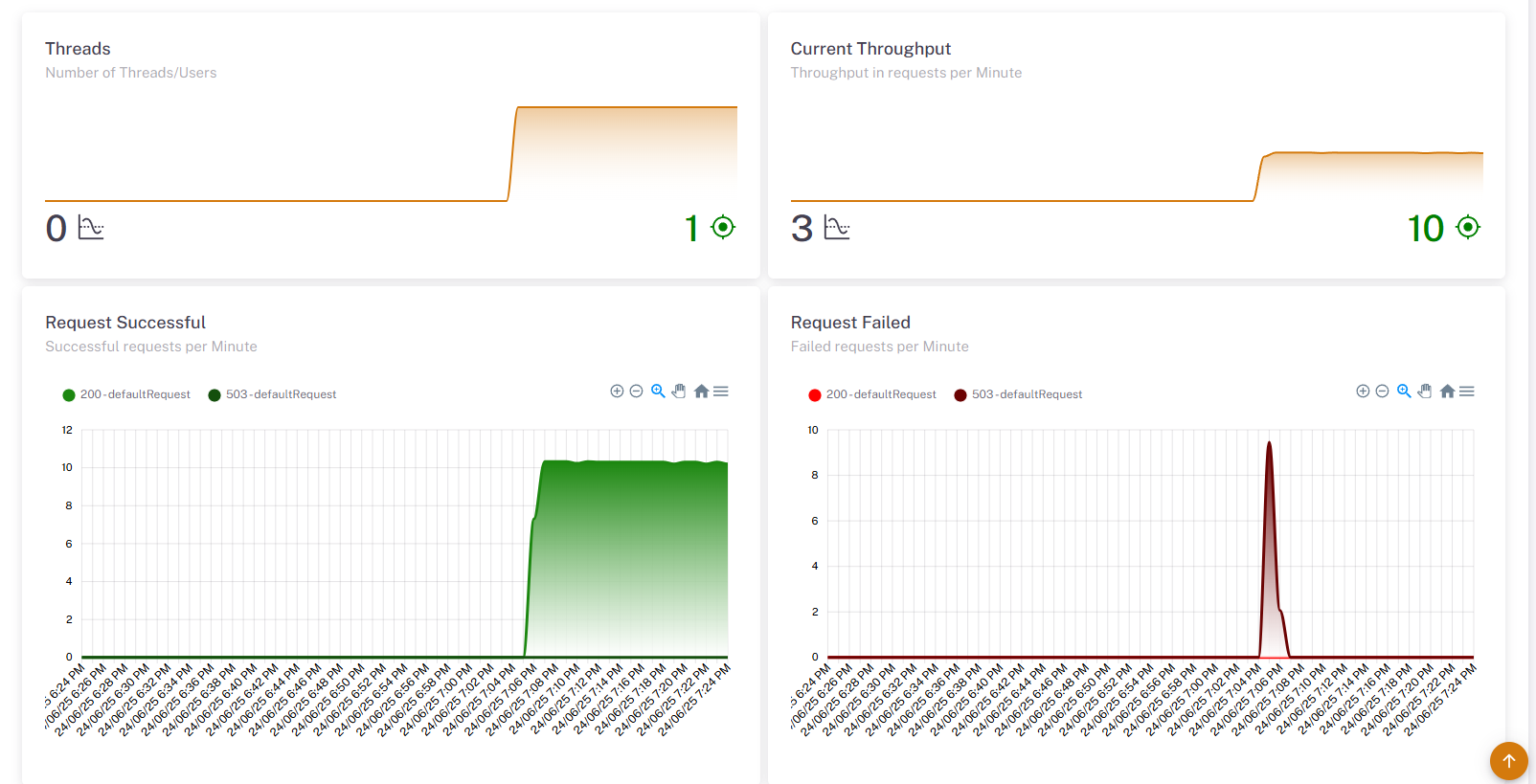
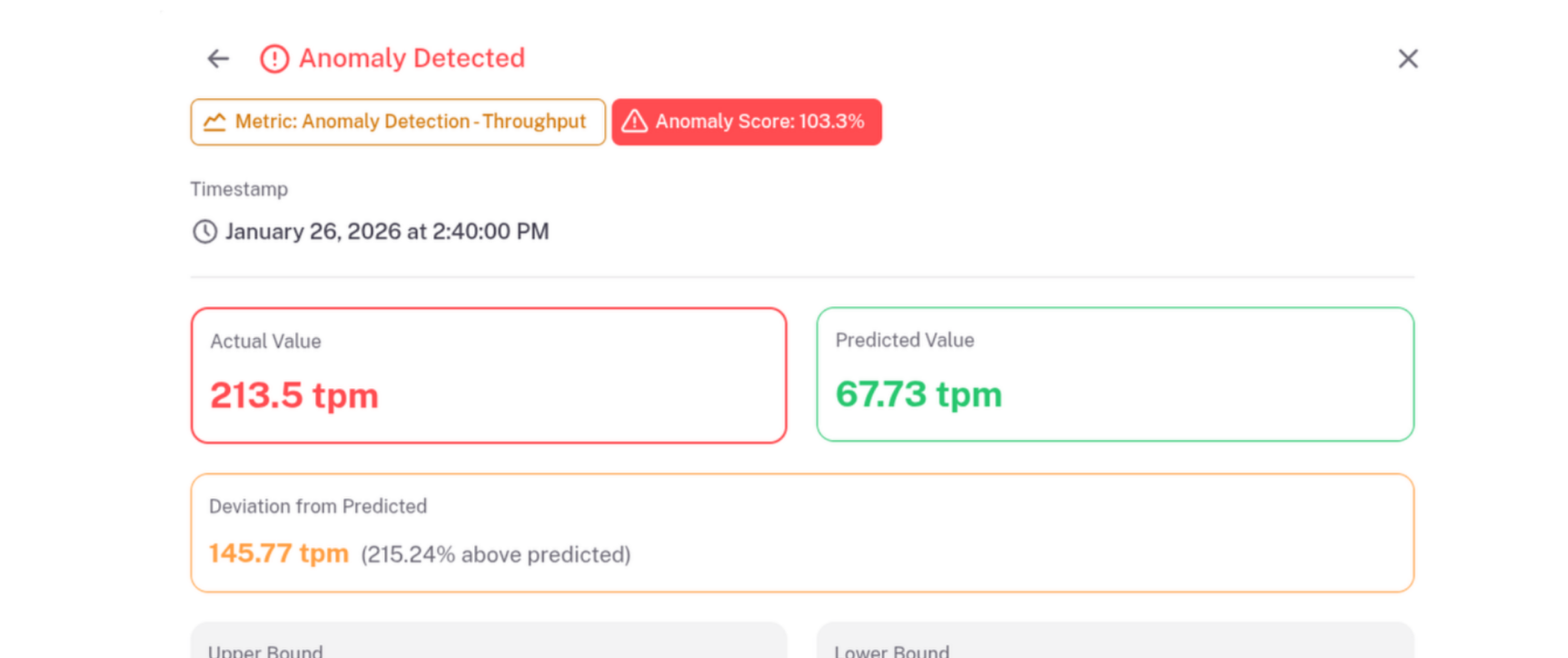
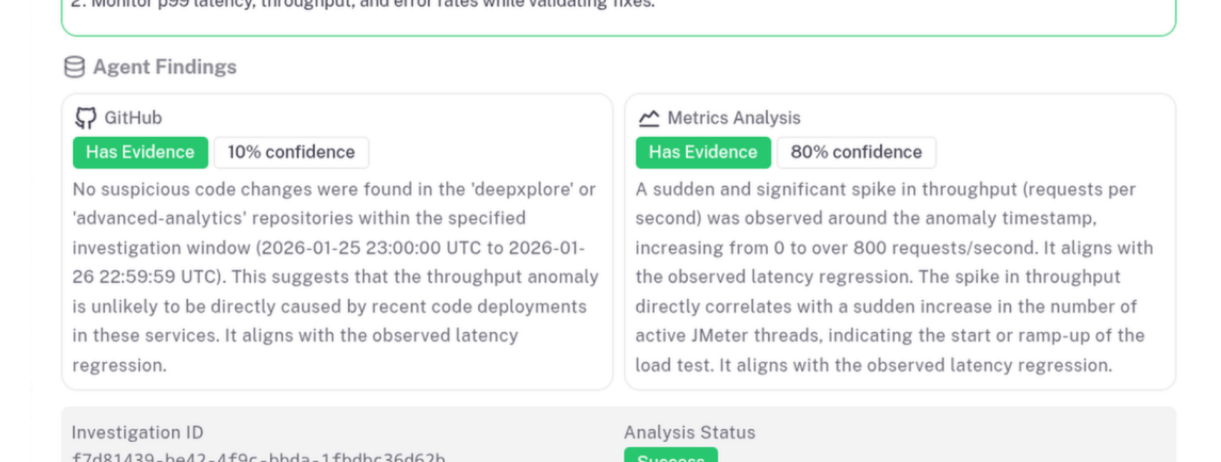
Comprehensive Reporting
Detailed insights into infrastructure performance across every test run. Track trends over time, compare against baselines, analyze system behavior, and produce reports that translate raw data into actionable decisions.